Developing Good Passwords
 ..
..
[December 2023] Cowboy has been involved in designing and writing computer programming and security for over three decades, including one of the first – and still rather effective – anti-spam filters. Unfortunately, he still sees many of the same security problems he wrote about 20 years ago, even as the bad guys have become more aggressive.
What makes a good password, you ask? Or are any old passwords good enough? You know what the Bard wrote: “A rose by any other name would smell as sweet.”
Actually though, you may be surprised – some passwords really stink!
PASSWORD POLICIES AND PEOPLE
Periodically, an on-line mailing list for broadcasters (the Broadcast list at www.radiolists.net) has a discussion about password practices – some good, some bad. Some of the experiences were, frankly, amazing.
Obvious passwords are bad – many hackers use what is called a “dictionary attack,” where they try every possible word (or combination), but strings of characters so complex they get written down are much worse.
For example, some company employees have e-mail, but often find they cannot access it – they seem to get locked out of their accounts regularly because they forget their passwords. Or how about the company with that uses a lengthy line of letters and numbers for the login and password, only to find the staff taping them to the studio monitors?
This is exactly why lengthy strings of random characters are a really, really, bad idea. Posted passwords are, in effect, no password at all.
BAD PASSWORD IDEAS
This is as bad as passwords like “password” or “123go.”
Many more examples are possible, such as anything a bank or credit card company has ever used. These would include your mother’s maiden name, any digits out of a social security number or credit card numbers, and addresses.
Worse, passwords that are complex are unlikely to change very often. Unchanging passwords in a world of three-gigahertz-plus speed password-crunching attack computers is not a good idea.
The exception would be machines that auto-logon and do not have number of character restrictions, like the individual’s company workstation, or roving profile. There, a 245-character “random” string that is entered once and never again seen by human eyes is entirely workable. Most likely, the machine will be replaced long before a password generator would have had time to crack it.
PASSWORDS FOR PEOPLE
Moving targets, like changing passwords, are much harder to hit. For human use, pass-phrases are much better, provided they are not too obvious. Something like The Quick Brown Cat Jumped Over The Lazy Fox Back – slightly changed, long, but easy for human memory.
Also good are apparently random strings derived from a pass-phrase, something like MBWbiO14 derived from “My beloved wife’s birthday is October 14” (This has the double-advantage of reminding one to buy that birthday present).
Of course, using the actual phrase as the password is better.
INTERNET CONSIDERATIONS
The use of actual phrases is definitely a good idea for any machines that are exposed to the Internet. The reason is that while any combination of “random” characters can be broken by a brute-force password generator, it is unlikely such a generator could re-create your phrase.
In many cases, a fair “generic” password would be something like the first and last letter of each word in the station slogan, in order, and including at least one real word. These things are easy to remember, yet difficult to decipher if one is not familiar with station operations or the details of an individual’s life.
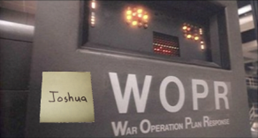
On the other hand, someone who is trying to crack your account might know some details of your life, so your child’s name is a bad idea. Remember “Joshua” from War Games?
Likewise, names of persons you admire, spouses, parents, etc. are bad choices.
It is also a not bad idea to change passwords anytime an employee leaves, for whatever reason. Anything taken from anything that would eventually end up in a trash can, like non-shredded credit card statements or old program logs, is a bad idea.
HOPELESS USERS
Of course, for the personality whose password is her own surname – and she manages to forget it at least once a week – there just is no hope!
This is one of the reasons on-air and other such mission-critical machines should be set up to auto-logon to whatever account is necessary to maintain normal operations – and this should not be the same as the account used for administration.
A password for a critical system, forgotten because it was a long string of unguessable random characters for “high” security, can be much, much worse than no password at all when that system goes down. Even a post-it note password will cause unnecessary delays in getting those machines back on-line and making money.
Of course, none of these machines should be exposed to the Internet without a very secure firewall between (and things like web browsing severely restricted), but that kind of system security is the crux of another article.
STOPPING PASSWORD CRACKERS
Most crackers will try a dictionary-type attack first, simply trying the more obvious permutations in common use, like password, PaSsWoRd, Passw*rd, letmein, letmein45, root, toor, etc.
It is not safe to assume that 14 characters are enough (because that was a common limit for Microsoft for many years), but it probably is sufficient unless a determined cracker uses the “brute force” automated generation of many random characters until they hit one that works.
By the way, most current brute force generators will normally filter and skip actual words, because it is well known that the common “random” password web sites do not generate real words. They also skip the common dictionary permutations.
I have often wondered just how secure it would be to use a combination of common permutations, separated by a few random characters, something like webmaster$#@root. The words will be tried by a dictionary attack, but the random characters probably will not. Similarly, the random characters would be tried in a brute-force attack, while the real words will not be used.
Oh, that bit on TV where the password generator ticks off single characters “found” to be part of the password? Pure fiction. I know of no system that signals pass or fail until the entire password is entered, rightly or wrongly.
PASSWORD POLICIES TO AVOID
Unfortunately, many on-line banking systems will signal that the user name was correct, but the password failed. What are they thinking?
Older Microsoft systems were known to work in reverse. Give them a valid password, and they do not even check the “user name.”
Pass-phrases and common words in uncommon combinations are far more secure than long strings of “random” characters. They will not be in the dictionaries and it will take a brute force attack years to hit that “random” combination – if it has been reprogrammed to include real words. If you have a cracker after you that is that determined, you have worse problems than simple net scans and weekend visitors.
SOME USEFUL IDEAS
In an air studio, where “talent” is not known for good password retention, I would recommend using something like the first and last letter of the names, both first and last names, of each person on the morning show.
Use their real names, not their air names, and include at least one real word; it seems in many situations that is about as good as it gets. If you find that they have written this down, it is past time to reconsider.
Another idea is something like the old authenticator list we used to get for EBS, where the password de jour changed daily. If the passwords on the list follow the above rules for combinations of words, this will be hard to beat, but has the disadvantage that no one can remember them, so they will be written down.
[the_ad id=”4306″]
REALLY STRONG PASSWORDS
In a data processing center or the IT department, if one wishes to get really secure and one can assume some degree of intelligence on part of the authorized people, passwords that change with time of day and date are almost impossible to crack, unless it is too obvious. Even then, a cracker has to know that this happens in that IT center.
Real good would be some easily manipulated algorithm that uses the date, and hour of the day in conjunction with a word list. Better would be for the words of the day to be generated by one of the machines and passed from shift to shift. Even written down, they will expire at the end of the day.
Something like the words apple and lawnmower taken from the daily list, then using the date and time – two time zones removed – can produce a password like apple714231217lawnmower for a station in Massachusetts when it is actually 2:17 PM on July 14 2023.
Perhaps the biggest dangerous from hackers is one you cannot control – and makes changing passwords from time to time a good idea: hackers breaking the hash code on a particular server because someone else used a flimsy password. This is discussed more fully here.
VPN PASSWORDS AND MFA
There are secure “VPN” type applications that generate passwords for each session.
What happens is the applications agree on a temporary password for the moment, encrypt and then use that secure channel to negotiate the password and encryption that will be used for that session. A caution: while this may be easy for machines, it may not be so good for the Traffic girl.
More and more systems are now incorporating MFA (Multi-Factor Authentication), where the system sends a text message with a one-time code. (For the three people in the world without a cellphone, some systems can call your number and “say” the code.)
We can wax poetic, but in the end the most secure passwords likely are those where you invent what method(s) or combination thereof that you will use – introducing a bit of randomness, you being you, into the methodology.
In the end, just keep in mind that simple, yet really secure, passwords are possible, but they are not going to come from random character generators.
– – –
Curt Flick is an engineer, programmer, and contractor based in Akron, OH. AKA “Cowboy,” he can be seen almost anywhere in the country as he works on a variety of broadcast station projects. Contact him at curt@spam-o-matic.net
– – –
Would you like to know when more articles like this are published? It will take only 30 seconds to
click here and add your name to our secure one-time-a-week Newsletter list.
Your address is never given out to anyone.

