Doing IT Right – Understanding Security for EAS Gear

Because the Emergency Alert System (EAS) equipment is required to be connected to the Internet, broadcasters have been introduced to all manner of security risks.
EAS devices are no longer isolated in the broadcasters’ operation – they are connected externally to monitor government sources of alert data, and are increasingly connected internally to interface with other broadcast systems. This is no different from many other key assets in a broadcast operation. Connections to the outside world create security risks. Security risks can come with a high price for broadcasters. However, many of these risks can be lessened with simple, straightforward steps to protect your networks, critical equipment, and company information.
On the other hand, attacks and breaches of your systems – including your EAS equipment – can cost time and money – including the disruption of regular business activities, costs to identify and correct the problem, or even the costs to the image and integrity of the broadcasters’ image. Taking a few steps to proactively improve your cybersecurity can save a broadcaster innumerable complications and costs. Commonsense steps to improve security can help protect critical broadcast infrastructure, business information, the integrity of the broadcast operation, and the integrity of the Emergency Alert System itself.
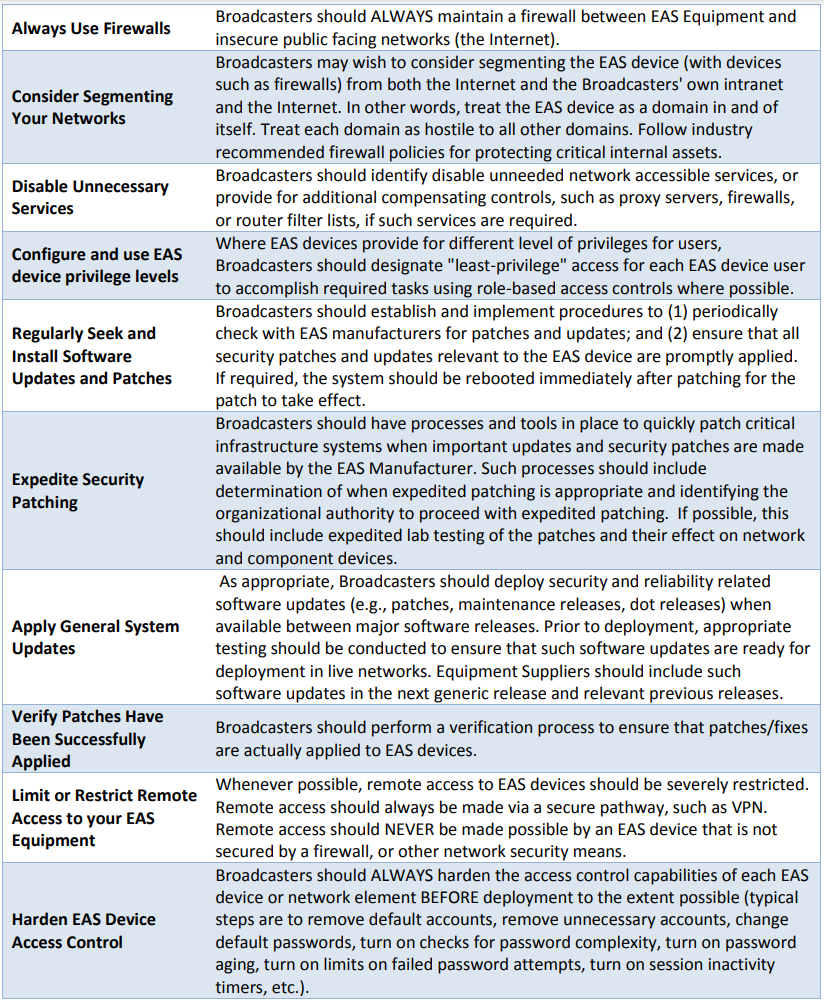
WHY YOU NEED A FIREWALL
EAS equipment is generally not designed as standalone security devices.
Simply stated, this equipment should never be exposed directly to the public Internet. Nor should any other key equipment in your broadcast operations be directly exposed to the Internet. This equipment must be utilized in conjunction with other network, physical and operational security measures.
The maintenance of EAS equipment presents a special role and responsibility, unlike many IT systems and devices. When properly used, the Emergency Alert System presents the opportunity to help safeguard the lives and property of citizens. On the other hand, if misused, attacked or exploited, the EAS could risk the safety of the public it was designed to protec.
For this reason, Digital Alert Systems has worked to present users of EAS devices with simple, commonsense cybersecurity best practices, to help guide both users in securing and protecting their EAS devices.
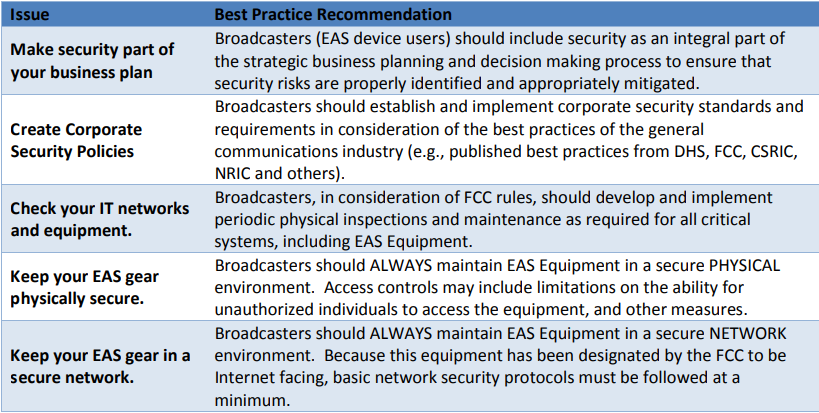
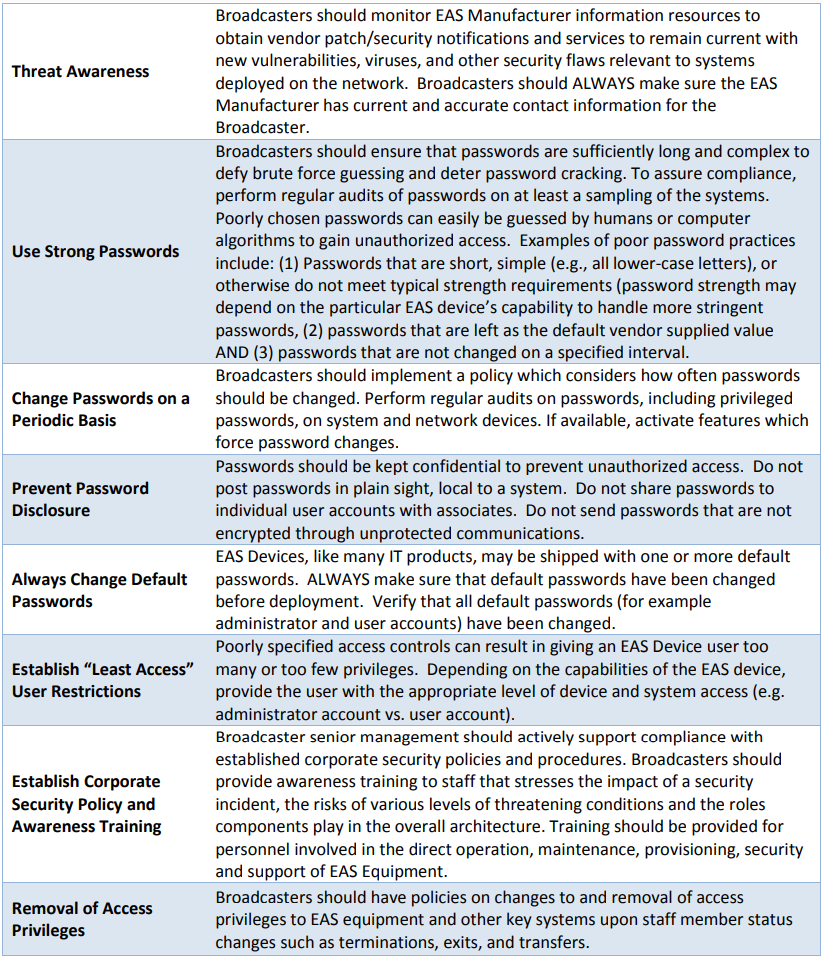
EAS Security Best Practices and Recommendations
Fortunately, security controls for EAS are by and large no different than security controls in any IT environment.
This includes your facility, network infrastructure and IT systems, and even the people that have access to this key equipment. We have developed a list of EAS Security Best Practices for Broadcasters, which provide a basic framework for broadcasters to assess their own respective cybersecurity readiness, to hopefully make informed decisions on areas of potential improvement.
These recommended best practices are built upon a growing body of knowledge that is available in multiple industry sectors, including numerous best practices generated by the Network Reliability and Interoperability Council (NRIC) and its successor, the FCC’s Communications Security, Reliability and Interoperability Council (CSRIC). References and a directory of resources are provided at the end of this document.
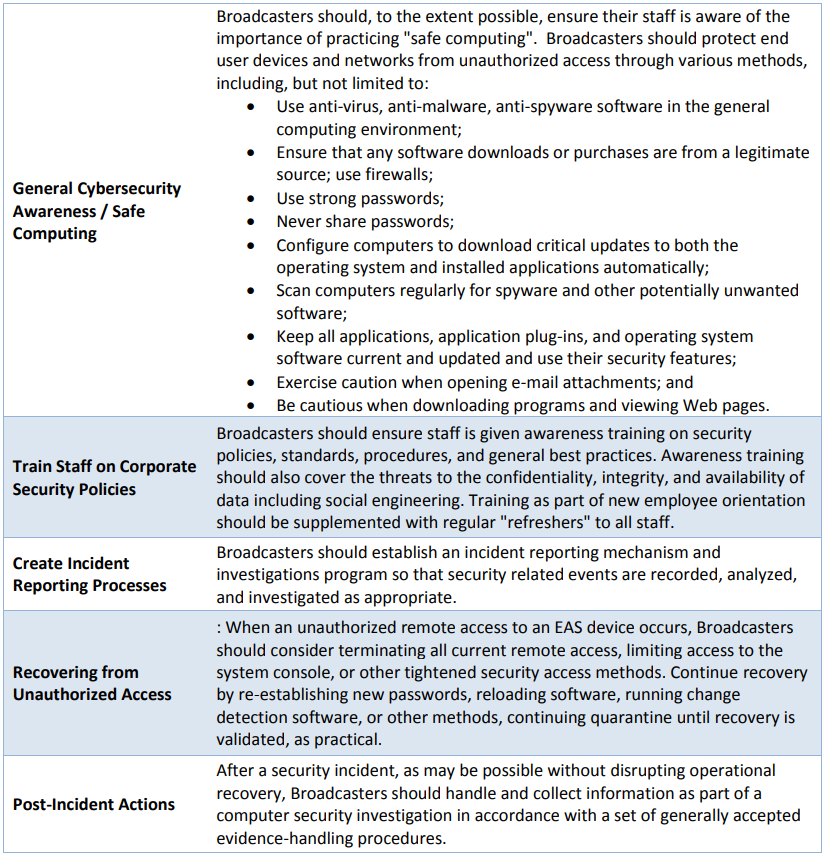
Recommended EAS Security Best Practices for Broadcasters
CONCLUSION
Cybersecurity is a critical dialogue, as the nation’s Emergency Alert System and related public warning capabilities increasingly leverage the Internet. A fuller understanding of the risks of poor security practices and taking corrective steps can help protect broadcasters’ critical assets, minimize risk, reduce exposure and potentially lower costs. A better awareness of the security issues, and the means to address them, can help protect the integrity and reputation of both broadcasters and the Emergency Alert System. By considering these best practices and how they may apply to your EAS equipment – as well as other key systems in your operation – you could benefit by:
- Increasing your own network’s reliability
- Increasing regulatory compliance by reducing risks of EAS device or system disruption
- Eliminating vulnerabilities and downtime costs
- Improving the performance of your critical systems
- Avoiding unnecessary costs associated from reacting to and recovering from a cyber incident.
– – –
The author is Vice-President – Strategy and Global Government Affairs with Digital Alert Systems, one of the major EAS providers in the US and Canada, and also serves on the FCC CSRIC and Canadian Common Look and Feel Committees. Contact him at: ed.czarnecki@digitalalertsystems.com
– – –
Are articles like this helpful to you? If so, you are invited to sign up for the one-time-a-week BDR Newsletter.
It takes only 30 seconds by clicking here.
– – –

